Not everyone knows that IIS (Internet Information Services), the webserver included in Windows Server, offers the possibility to perform mutual authentication using SSL certificates.
You probably saw that, within the site’s SSL configuration, you can require an SSL client certificate to the client that is connecting:
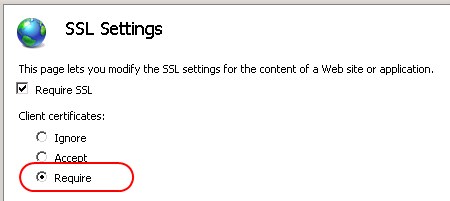
in this case, IIS only verifies that the submitted certificate is valid, i.e. signed by a trusted CA.
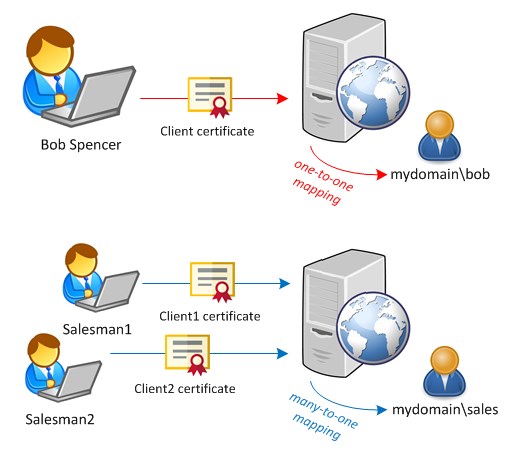
The mutual authentication allows you to go one step further: based on the certificate that the client sends to IIS, the server maps it to a local or domain user. It is therefore possible to identify a user without requiring username and password, but based on the certificate it owns.
IIS allows two different mappings: one-to-one (each certificate corresponds to a specific user) or many-to-one (multiple certificates correspond to a single user). In the first case you have to load the whole certificate in IIS, while in the second one you indicate to IIS the characteristics that the different certificates must have (for example the value of CN):
Configuration
You cannot configure the Certificate Mapping via graphical interface (IIS Manager); the configuration is possible only directly modifying the IIS configuration.
First verify that the following role services are installed on your server:
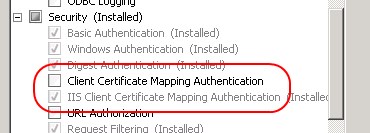
the first one (Client Certificate Mapping) is used for mapping clients to domain accounts (Active Directory), while the second one (IIS Client Certificate Mapping) for local accounts.
Open the configuration editor of the website you want to modify:

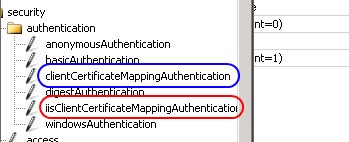
The configuration of both modules is under security – authentication:
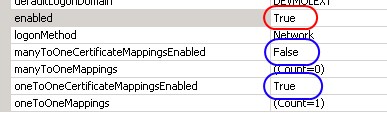
For example let’s configure the mapping on local accounts. First you have to enable the module and choose if you want one-to-one or many-to-one mapping (you can enable both):
To add a one-to-one mapping, click on …:

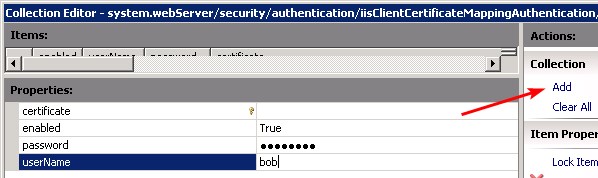
then click on Add and type the requested information (certificate, username and password):
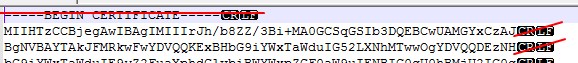
you have to provide the certificate in base64, after having removed the lines —BEGIN CERTIFICATE— and —END CERTIFICATE— and the new line characters so that all the content is on a single line:
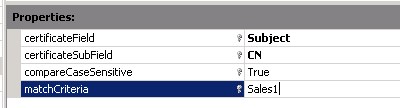
The steps to add a many-to-one mapping are similar… instead of loading the certificate you have to define one or more rules. If the client certificate matches a rule, the mapping is performed:
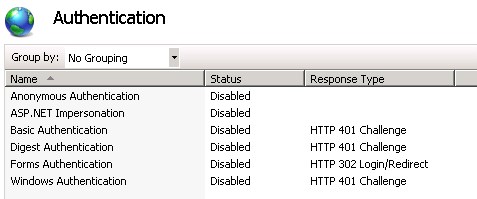
As last step, remember to disable the other authentication methods:






Ciao, complimenti per la ottima guida. Ho un dubbio, però: cosa sono le username e password da inserire nella configurazione del mapping? Cioè, la premessa che fai all’inizio è “E’ quindi possibile identificare un utente senza richiedere username e password, ma basandosi sul certificato che questo possiede.”. Quindi a che servono username e password? Grazie.
Ciao Roberto! Una volta autenticato tramite certificato, chi si collega deve “impersonare” un utente di sistema (ad esempio per poter accedere ai files del server…). E’ quello il motivo per cui devi associare il certificato (= la chiave di accesso) ad un utente (e relativa password) locale o di Active Directory.